Tor browsers create encrypted entry points and pathways for the user, so dark web activity remains anonymous. The encryption technology routes users’ data through a large number of intermediate servers, which protects the users’ identity and guarantees anonymity. When exploring the invisible web, ensuring that your tools work seamlessly with privacy-focused technologies is essential. Many deep web search engines and browsers rely on specific configurations to maintain your anonymity.
How To Safely Access The Best Dark Web Sites – Quick Guide
Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are. Your traffic is relayed and encrypted three times as it passes over the Tor network. Before exploring, make sure you’re familiar with the laws in your jurisdiction.
How To Access The Dark Web
This service lets you create your unique domain name with the letters or words you prefer. The site isn’t dormant; you can still find some of their old and very interesting blog entries and helpful resources. But we are on the dark web, you can’t trust anyone, so there may be sites containing illicit content.

Onion Links To Deep Web Email Services
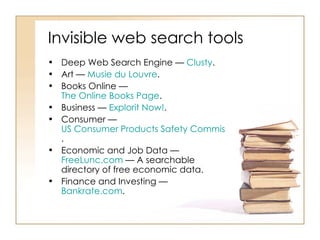
Haystak does not censor content by default but provides safety flags to help users make informed decisions. Since regular search engines don’t index .onion sites, finding what you need on the dark web can be tricky. That’s where dark web search engines come in — they help you discover hidden websites and make navigating this part of the internet easier. In this guide, you’ll find the top 9 dark web search engines, complete with .onion links.
The Dark Web refers specifically to websites and services hosted inside Darknets. Search engines do not index these sites and use domains like .onion (for Tor) or .i2p (for I2P). Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from … Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr…

Imperial Library
Consequently, users benefit from a constantly evolving tool that adapts to their needs. If you’re having trouble opening a specific onion link, or the overall Tor speed is slow, we have detailed tips on how to make Tor faster. Of course, bypassing paywalls is ethically questionable and may be illegal in some jurisdictions. That’s why many people choose to do so anonymously on the dark web, rather than using the clear web version of the site. Since academic research is often fenced off behind paywalls, Sci-Hub aims to democratize knowledge by allowing people to see publicly-funded research for free.
DuckDuckGo (Dark Web Version)
Unlike many imitators, this is the official Hidden Wiki that maintains a curated directory of legitimate .onion services. During my testing, I found its categorized index particularly helpful for discovering trustworthy sites across various topics. Viruses, ransomware, and other types of malware are more common on onion sites than on the normal internet.
Directory Of Open Access Journals – Best For Researchers And Academics
Plus, many .onion websites are created to be temporary or invite-only, so they may not even be active long enough to be indexed. With solutions like Brandefense’s Dark Web Monitoring and Threat Intelligence, businesses can detect threats early, respond swiftly, and safeguard their digital assets. Whether you’re a business looking to protect your assets or an individual prioritizing online privacy, Brandefense ensures you’re always secure in the digital shadows. Phobos is a very minimalistic and simple search engine for Tor .onion hidden websites. Like Google, you type the keyword you are searching for, click on search, and that’s it.
Use categorized directories or reputable search engines to reduce the chance of clicking on spam or malicious links. Avoid sites that require JavaScript activation or make suspicious requests. Never share personal data such as your name, IP address, email, or financial information. The dark web’s anonymity is one of its primary security features, and violating it can make you a target for identity theft or phishing. Although they all serve a similar purpose, these search engines differ significantly in terms of usability, safety features, and how they index content. At a technical level, these engines access the dark web using specialized protocols, like the Tor project.
It’s a hidden layer of the internet beyond the reach of traditional search engines. However, business leaders and security professionals can no longer afford to ignore this part of the internet. While traditional security tools focus on known threats, some of the biggest risks, like data breaches, identity theft, and corporate espionage, often start out on the dark web.
You are not required to provide your personal information to create an account. The email service is available both on the surface and on the dark web. In some countries, such as China and North Korea, the government uses heavy online censorship and blocks many dark web websites. This is where an Onion website, like the Tor browser, comes in handy. The social media giant is also aware of the many attempts by repressive regimes to restrict its access.
Veridian aims to provide a single portal to all the historical newspapers of the world. It’s a fantastic resource for researchers—especially family historians, genealogists, and students. Your ISP, and possibly the authorities, may decide to start monitoring your activity more closely to look for threats or illegal activity.
The service remains free to use, and the secure design prevents access to third parties, eavesdroppers, and other malicious agents. Some countries and ISPs may try to prevent access to DuckDuckGo’s direct link. AVG Secure VPN encrypts your internet traffic and obscures your IP address every time you use it to go online — dark web or not.
- Stay private with a tool like Surfshark’s Alternative ID to mask your contact details and use generated data on sites you don’t trust.
- It’s a lesser-known but highly effective unrestricted search engine ideal for in-depth exploration.
- This disables potentially dangerous features like JavaScript that could reveal your identity.
- It stands out for not tracking user activities or saving search histories, ensuring a private browsing experience.
- Before exploring, make sure you’re familiar with the laws in your jurisdiction.
Duckduckgo – Best Service To Dip Your Toes Into Deep Web
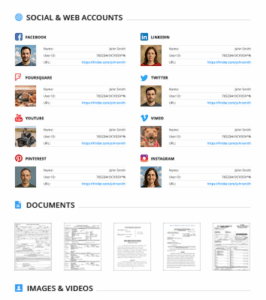
However, using sites like Spokeo should only be done with the best of intentions. Claiming to have access to more than 12 billion public records, Spokeo is a great place to start for reverse phone number checks. Ahmia promotes transparency by being open-source and allowing contributions. Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network.
- Here’s a breakdown of the most commonly used dark web search engines in 2025.
- The most common method to access the dark web is through the Tor network, which uses the Tor Browser.
- Regular search engines only provide results from the most recent version of a website that’s available.
- For the record, there are more scam sites for every genuine one, and it’s good to have a discussion forum about this.
Quick List Of The Best Dark Websites In 2025
Watch for unexpected changes in system performance that could indicate malware. Cryptocurrency miners and other malicious software often target dark web users. Using a reliable antivirus to scan your device is worthwhile if you spot suspicious spikes in system resource usage. This isolates any potential malware and prevents cross-contamination with your personal data.