In the volatile world of dark web marketplaces, longevity is never guaranteed. Atlas Market shows promise with...
The deep web is made up of email platforms, workplace portals, subscription services, and banking websites —...
It was touted as a major policing win and was accompanied by a slick cyberpunk-themed video. When...
For a number of technical reasons, it’s much faster and more reliable than Tor. The peer-to-peer routing...
Surprisingly, most guns on the darknet actually start as legal products. The UNODC (United Nations Office on...
To access this marketplace, you must register, but before that, you must verify yourself as a human...
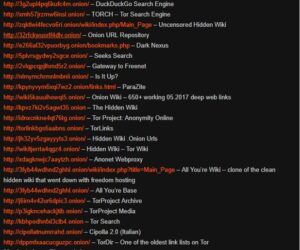
Many onion sites provide valuable resources such as news, secure communication, and educational materials. Despite its reputation,...
The surface web (often referred to as the “visible web”) is the portion of the web available...
There might be malicious nodes with the Tor network, and there’s always the risk of your IP...
It is not indexed by standard search engines and contains both legitimate and illegal content. The “Dark...