These stolen cards have value because they can be used to purchase expensive items or gift cards, which can then be resold for cash. This process is known as “carding”, and it has become a key part of the cybercriminal’s playbook. The technique is very profitable in its own right, but it is also used to help launder and cash-out cryptoassets obtained through other types of cybercrime. UniCC has been active since 2013 with tens of thousands of new stolen credit cards listed for sale on the market each day.
As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web. There are often copious amounts of how-to articles, software exploits, and hacked credentials for sale. Not every visitor is a criminal, but this is where most cybercrimes begin.
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session.
Best Dark Web Sites: Unseen Onion And Tor Links
This website is made public with the intention to aid the Internet users with navigation of the so called dark web. We have never received a compensation in any form for operating this website. We are not responsible for any harm or loss you may receive by following links listed on this site. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. These domain names are not registered with a central authority but are instead derived from cryptographic keys.
Nexus Market

Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services. Some markets even sell privacy tools, but you are more likely to run across counterfeit prescription pills and stolen identities. Some markets are relatively short-lived (thanks to law enforcement), but others are notorious enough that they survive, for instance, Silk Road, AlphaBay, and Hansa.
Which Type Of Credit Card Is Worth The Most On The Dark Web?
Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. However, there are some significant variances in the background despite the similarities. For example, Whonix’s virtual workstation machine connects to the internal virtual LAN. It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address.
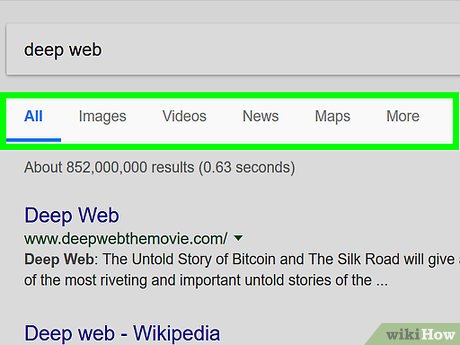
How To Access The Dark Web
They know how to process the information and get it to the correct law enforcement agencies internationally. Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators.
Navigating Dark Web Marketplace Links
It aims to preserve the internet’s scientific and cultural heritage. SecMail is one of the most popular email services on the dark web. While this is not much compared to standard email services, it is enough for PGP-encrypted messages. The goal of an anonymous and privacy network, Tor, is not to engage in the extensive collection of data. However, data is required for understanding, monitoring, and improving the network. Furthermore, data will help to detect attacks against the network and possible censorship events.
Criminals Are Selling Millions Of Stolen Credit And Debit Card Numbers On The Dark Web
These layers upon layers give this network its iconic “onion” name—as the onion itself has layers upon layers. When you try to enter a .onion website, it will reroute your access request around the internet, bouncing it off three random servers before you reach the target website. Like regular browsers with domain names, the Tor browser also has its own domain designation. These “onion” sites are only accessible on the dark web and bear the “.onion” domain at the end of the URL. This is no different from the “.net” or “.com” of the regular Internet.
- Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash.
- The technique is very profitable in its own right, but it is also used to help launder and cash-out cryptoassets obtained through other types of cybercrime.
- As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of.
- The anonymity provided by onion routing comes at the cost of slowing your internet considerably.
You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search.
The users on this site can review and rate the products that promote reliable and fraudster vendors. Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here. The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them. You can see all the product categories the marketplace deals with on the homepage. Like other marketplaces, it also requires registration for new users and accepts payments in Monero.


The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web. You can also run a dark web scan to see if your information has been leaked on the dark web. This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.



