
One of the most dangerous aspects of the Dark Web is its potential to facilitate large-scale cyberattacks. Hackers can purchase everything from stolen data to zero-day vulnerabilities (security flaws in software) that allow them to exploit systems before the vulnerabilities are patched. Cybercriminals often use the Dark Web as a platform for data breaches, identity theft, and fraud. Stolen databases from large corporations and government agencies are frequently sold to the highest bidder. Hackers also use the Dark Web to exchange tools, tips, and techniques for breaching computer systems, creating a thriving ecosystem for cybercrime.
Risks Of The Dark Web
The Dark Web is a hidden part of the internet, completely different from the clear web we all use daily. When you search for something on Google or Bing, you’re using the clear web. That said, many of the actors on the dark web are highly skilled digital adversaries who can easily outmaneuver basic security measures. As a leading cybersecurity vendor, CrowdStrike cautions all organizations and individuals to refrain from using the dark web. The dark web continues to be a valuable tool and exchange network for many groups around the world.
Best Browsers For Accessing The Deep And Dark Web
Suppose you share your name, social security number, or any other personally identifiable information on any dark website. In that case, there is a high chance that your data will become accessible to cybercriminals. Then, they can use your data to impersonate you and run social engineering attacks to target your loved ones. Using a VPN alongside Tor adds an extra layer of security by hiding your IP address from Tor entry nodes and encrypting your traffic. This prevents anyone—including your ISP—from knowing that you’re using the Tor network. You might visit the dark web seeking anonymity or unique services, but this anonymity also attracts scammers.
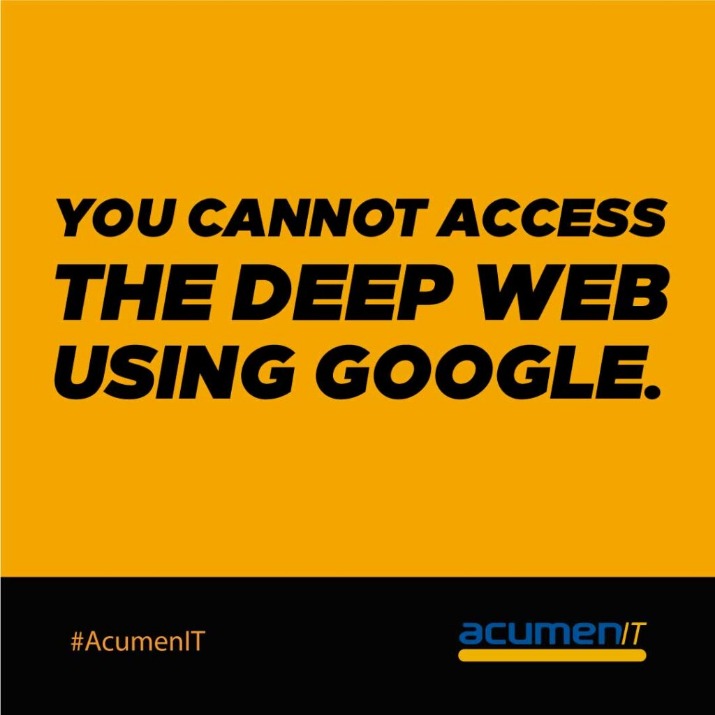
Can Search Engines Like Google Access The Deep Web Or Dark Web?
It does support whistleblowers by offering them anonymity and secure communication in an oppressive regime. But navigating the dark web is full of cybersecurity and legal challenges. While Tor lets you reach .onion sites, many require invitations, passwords, or verification.
- As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others.
- However, while visiting the dark web itself isn’t against the law, engaging in illegal activities there is.
- Meanwhile, Facebook also offers dark web access to their social network.
- The deep web refers to hidden web pages that are not indexed by search engines.
- Cloudwards.net may earn a small commission from some purchases made through our site.
CrowdStrike Global Threat Report

Identity theft monitoring is critical if you want to keep your private information from being misused. Passwords, physical addresses, bank account numbers, and social security numbers circulate in the dark web all the time. You may already be aware that malicious actors can use these to harm your credit, engage in financial theft, and breach of your other online accounts. Leaks of personal data can also lead to damage to your reputation via social fraud. Web pages on the Dark Web can only be accessed using the Tor browser, and users need to know the URL of the website to find it. This makes Dark Web sites a rich source of threat intelligence for organizations; however, the design of the Dark Web can make this information difficult to find.
Its operations focus on respecting user privacy and maintaining anonymity through the use of the Tor network. The security implications of the surface web differ significantly from its hidden counterparts. However, it poses challenges for collaboration; sharing Deep Web resources across organizations requires secure, standardized protocols. Great life advice, but it’s even more valuable where the darknet is concerned. Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly.
What Is The Dark Internet?
Tails always starts with a clean slate and any evidence of the activities you engage in while using Tails disappears when you shut down Tails. This includes evidence of any websites you visit, files you open, passwords you use, and even any other devices or networks you connect to. Tails never writes anything to the computer’s hard drive, running only from the RAM of the computer, which is wiped clean when the computer is shut down. Users who wish to gain access to such information are protected by the same anonymity the publishers of the content enjoy. Well-known news websites, such as ProPublica, have launched deep websites.
- This article reveals the top five key differences between the dark web and the deep web.
- Because of their anonymity, dark web sites are breeding grounds for illegal activity and transactions.
- Websites that exist purely on the deep web have different access, so there’s a level of privacy for the website hosts that isn’t possible on the regular internet.
- Examples include software as a service (SaaS) solutions, paid news websites, and streaming services.
RiseUp — A Secure Email And Chat Platform For Activists
We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Absolutely no one knows who’s surfing on the dark web, who is selling, who is buying or anything like that – as long as you take the correct safety and online privacy precautions. Silk Road became one of the most famous online black markets on the dark web for illegally selling drugs. So, that means that the number of pages increased by over 100 trillion in just over three years.
Although they share similarities, these parts of the internet serve very different purposes. Knowing the difference between the Deep Web and the Dark Web is vital for online security and privacy. Silk Road was a pioneering darknet market, established in 2011 by its founder Ross Ulbricht who was known as ‘Dread Pirate Roberts’ in online circles. Managed entirely on Ulbricht’s personal laptop, this online black market facilitated a slew of illicit transactions until it was shut down by the FBI.
How To Stay Safe On The Dark Web
That’s why, as cybersecurity experts and safety advocates, we don’t recommend accessing the dark web. As we all know, websites on the surface web end with common suffixes such as .com, .org, .edu, and .gov. When browsing through Tor on the dark web, however, the suffix is .onion. It’s fitting because Tor itself stands for The Onion Router, a reference to the multilayered (like an onion’s skin) encryption it uses to keep users anonymous. The answer, of course, is by using dark web browsers like the open-source platform Tor. A repository of sites that can’t be found by traditional search engines, the dark web is as intriguing as it is dangerous.
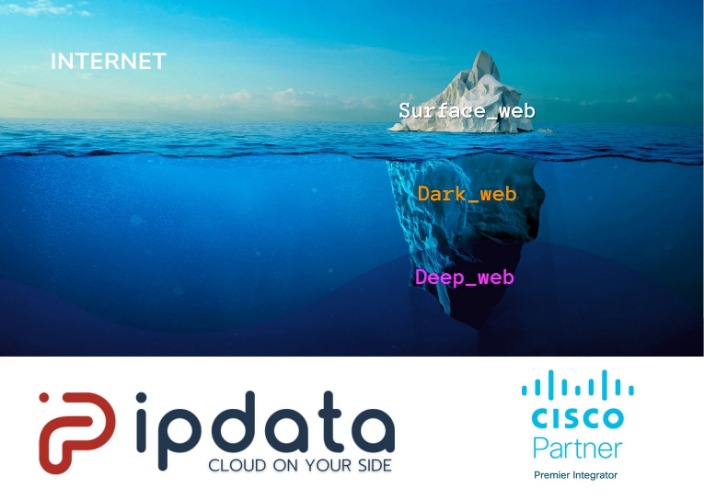
Ratings are easily manipulated, and even sellers with long track records have been known to suddenly disappear with their customers’ crypto-coins, only to set up shop later under a different alias. That said, anonymity comes with a dark side since criminals and malicious hackers also prefer to operate in the shadows. For example, cyberattacks and trafficking are activities that the participants know will be incriminating. The dark web, however, is a very concealed portion of the deep web that few will ever interact with or even see. In other words, the deep web covers everything under the surface that’s still accessible with the right software, including the dark web. Venturing further into the deep web does bring a bit more danger to the light.
What Types Of Content Exist On The Deep Web?
Each time you connect to a dark web link, your request and traffic are routed through at least three different server points, ensuring your IP remains hidden. Dark.fail is an easy-to-use .onion platform equipped with a status checker that tracks website uptime. The site offers access to PGP-verified URLs and runs free of JavaScript or tracking.
What Is The Dark Web, What’s On It & How To Access It
Thankfully, you don’t need to use your official name or email; just use a fake username (we tested it successfully). The site doesn’t require an email verification, though it offers all the features and security that you want in a dark web marketplace. Few countries operate with strict censorship on citizens’ internet access, preventing them from getting information in or out. BBC is the most popular news source and is the best example of restrictions on International media.
You might fall to the wayside of legal lines for many reasons that are important for the protection of freedom. Others may act in ways that are illegal for the protection and safety of others. Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves. The dark web refers to sites that are not indexed and only accessible via specialized web browsers. Significantly smaller than the tiny surface web, the dark web is considered a part of the deep web. Using our ocean and iceberg visual, the dark web would be the bottom tip of the submerged iceberg.
In the shadows of the internet, the dark web remains a complex and multifaceted entity. While it offers unparalleled privacy and freedom, it also requires vigilance and caution. By understanding its structure and ensuring safe browsing practices with tools like Forest VPN, we can navigate this digital underbelly responsibly. Whether you’re exploring for curiosity or necessity, the dark web reminds us of the dual nature of technology—empowering yet enigmatic. Most internet users access the deep web almost every time they are online. It is tremendously more vast than the surface web, with some experts estimating that search engines index less than 1% of online content.



