We have simplified the cybersecurity assessment process and made it accessible for all businesses. This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web. The market is known for its extensive product listings and reputation system that helps buyers evaluate the reliability of vendors. The platform is favored by cybercriminals seeking access to accounts that can be exploited for fraud or sold to others. Here’s a look at the top 10 dark web markets currently dominating this underground space. Markets that lack proper security often become targets for law enforcement, scammers, or cyberattacks.
Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity.
What’s For Sale On The Dark Web (and How AI Is Changing The Marketplace)
Last year, Kaspersky experts witnessed a significant uptick in stealers and extortion activities on the dark web market. Advanced monitoring services like CyberNod offer businesses a critical defense, alerting them to potential leaks and helping protect their assets. By keeping a vigilant eye on dark web activity, CyberNod provides early warnings of compromised data, empowering businesses to take proactive measures to secure their information. We showed that a small fraction of traders is responsible for a large fraction of the trading volume, and by analysing the networks of buyers and sellers, we found different resilience regimes. Shocks tend to induce serious structural changes in the multiseller network, but impact the multibuyer network much less severely.
The first ever DNM — called Silk Road — was started in 2011 by U.S. citizen Ross Ulbricht. While it included some innocuous listings such as health supplements, the majority of vendors and most of the sales were related to illicit drugs. Silk Road not only aggregated thousands of drug vendors, it created a user-friendly interface that resembled a clear-net shopping website. Ulbricht was eventually arrested by US law enforcement and Silk Road was seized and taken offline. Marketplaces that maintain strict moderation policies—banning excessively harmful or exploitative products—also gain popularity among more ethically minded users.
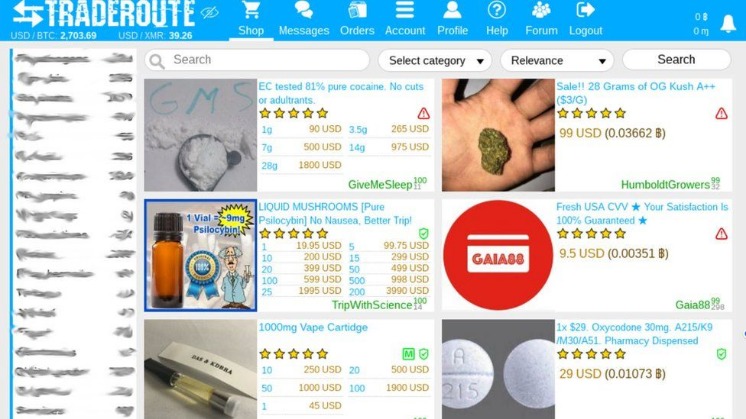
Some listings are nothing more than scams designed to trick people into sending cryptocurrency without delivering anything in return. Many listings involve stolen personal information, including credit card data, Social Security details, and full identity profiles. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails.
The Birth And Rise Of The Silk Road
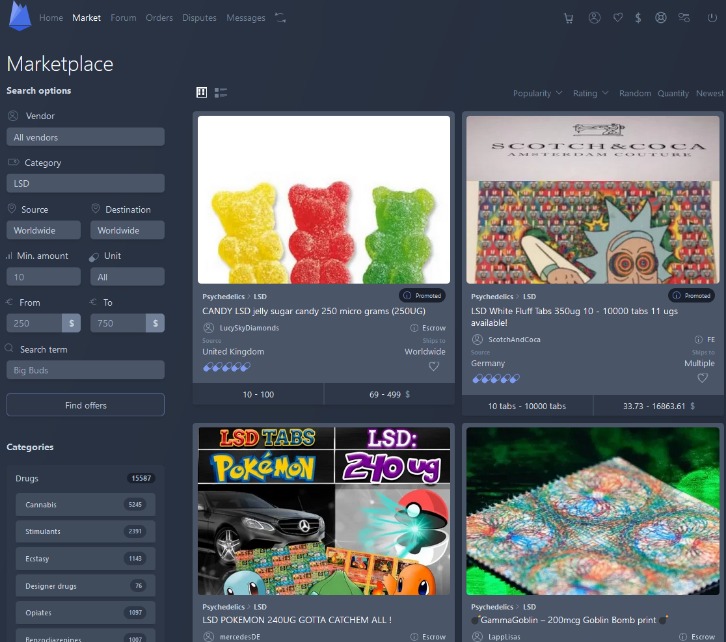
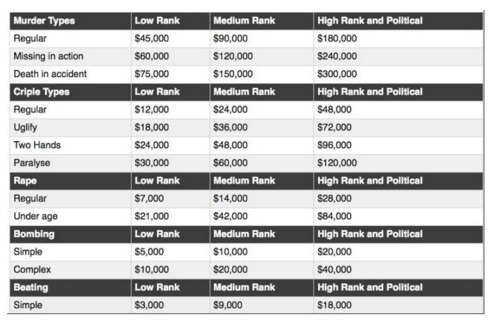
On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals. They provide criminals with access to everything they need, from launching attacks to stealing data, etc.
What Was The Silk Road Dark Web?
- Dark web marketplaces remain a persistent threat, enabling the trade of stolen data, hacking tools, and other illicit goods that directly impact businesses of all sizes.
- Understanding how cybercriminals profit on the dark web and how AI has fundamentally changed the game is essential for IT professionals developing effective defense strategies.
- The site looks sharp, and vendor profiles are packed with ratings and reviews.
- To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers.
- 7, we show the largest component of the S2S network one year before the operation Bayonet and one year after.
- They lure crypto users to scam sites and Telegram bots under various guises, and add crypto-stealing functionality to infostealers and banking Trojans.
Since 2020, 2easy has sold massive stealer logs with sensitive data like passwords, bank cards, and initial access credentials. It supports operations in multiple languages and operates on both clearnet and Tor. One of the biggest problems cybersecurity teams face isn’t a lack of tools — it’s too many alerts. And beware—while many explore out of curiosity or for research purposes, it’s important to remember that engaging with these platforms, even as an observer, can lead to serious legal and ethical consequences. Whilst a great many products are sold, drugs dominate the numbers of listings, with the drugs including cannabis, MDMA, modafinil,108109110 LSD, cocaine, and designer drugs.
Deep Dive Into Darknet Markets Of 2025
It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily. That means that Google wants to minimize the amount of time users spend searching for certain queries.
Stealers And Drainers To See A Rise In Their Promotion As Services On The Dark Web

The dark web comes with its own set of tools and services, including web browsers and search engines (which I’ll get on to in a moment). Part of what makes the dark web the dark web is that you can’t access it through your normal web browser, nor can you look something up on it via a Google search. Even though DuckDuckGo is the Tor browser’s default search engine, it doesn’t index dark web websites, which means you won’t be able to find .onion sites with it. It is a useful tool for people who value their privacy and want to protect their communications with default end-to-end encryption, zero-access architecture, and minimal personal information requirements.
So What Is The Darknet, Exactly?
After AlphaBay closed, Abacus Market took its place as the world’s largest underground darknet marketplaces. Abacus Market quickly rose to prominence by attracting former AlphaBay users and providing a comprehensive platform for a wide range of illicit activities. Still, even with these crackdowns and better defenses, dark web markets just keep coming back. As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down. User reviews and vendor ratings play a critical role in maintaining trust within these markets.
The site gives out free samples of the stolen data every now and then to gain more customers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one. One of the things STYX is infamous for is having a rigorous verification process for users that makes it seem more exclusive. They even have a Telegram channel to provide their clients with live updates. Like most of the markets, STYX supports Bitcoin (BTC), Monero (XMR), and other crypto tokens to keep everyone’s identity hidden on this marketplace. These marketplaces are full of risks (security, legal, ethical issues – all of them).
Some vendors offer “stealth shipping” guarantees, ensuring products are discreetly packaged to avoid detection. In addition to its emphasis on stolen credentials, 2easy Market offers a variety of cybercrime tools, such as hacking services, exploit kits, and other resources for conducting cyberattacks. These features help establish trust between buyers and sellers, providing users with a sense of security that many other markets lack. With its low 5% vendor fee, secure transactions, and verified sellers, it’s an ideal choice for buyers looking for a trusted marketplace. The key differences between dark web markets and regular online stores are clear.

Alternative Anonymous Networks
Each marketplace is a star-graph where the central node is the marketplace, and the leaf nodes, i.e., the first-neighbors, are the marketplace users. Therefore, all transactions involving the market have the market either as a source or as a destination node. To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13. The trading volume generated by stable pairs is more than five times larger than that of non-stable pairs13.
The anonymity and lack of rules that define darknet marketplaces are exactly what make them breeding grounds for fraudulent activities. Of course, the promise of secrecy and unfiltered access might lure you in, but those same features are what make the environment so risky. Unlike regular e-commerce sites, markets on the dark web often deal with illegal or highly restricted goods and services, such as fake documents, hard drugs, and hacking services. Sure, you might come across listings for legit products like handcrafted jewelry or digital art, but those are few and far between. The demand for pharmaceuticals on darknet markets remains high, with a focus on prescription medications, nootropics, and performance-enhancing drugs. These products are often sourced from international suppliers, ensuring competitive pricing and a wide variety of options.
Implementing strong authentication protocols, such as multi-factor authentication (MFA), significantly reduces the risk of unauthorized access. MFA requires users to provide multiple forms of verification, such as a password and a one-time code, making it more difficult for attackers to exploit stolen credentials. A 2023 IBM report found that the average cost of a data breach exceeded $4.45 million globally, with SMEs disproportionately affected.