“USDH is not restricted by traditional regulatory agencies,” read one promotion for the currency. Additionally, it’s built its own messaging app called ChatMe, which replicates many of the features of Telegram, said Elliptic. That could indicate a move away from billionaire Pavel Durov’s app, which has started providing a lot more data to law enforcement in recent months since its founder was charged with allowing child exploitation on his platform. In addition to some of the differences between the experience levels and type of activity seen on forums versus Telegram, there is also a key difference between the accessibility, user interface and technical requirements in order to join the communities.
In addition to facilitating the purchase of fake engagement, 39 channels shared images that served as proof of successful service, likely to build trust among potential customers. These images demonstrated the effectiveness of the service, showcasing increased engagement as a result of purchasing the services. Figure 6 shows a channel displaying proof of a successful Instagram follower purchase, which visibly increased the follower count. As our previous two blogs established, Telegram is home to very active markets of cybercriminal activity.
Top Drug Vendors
Telegram offers users similar levels of privacy if they opt to create a “Secret Chat” which uses the same end-to-end encryption that those apps do. It means the activity inside a conversation is completely private and not even Telegram itself can view the contents. This channel highlights how stolen financial data circulates through the Dark Web and Telegram, reinforcing the platform’s role in the distribution and monetization of illegal information. Some posts even display full card numbers and financial details, clearly showing the level of exposure these data sets face online.
These forums are typically dominated by a small group of experienced members who share a range of illicit resources (Afroz et al., 2013). Consequently, many cybercriminals have turned to alternative platforms such as social media, which provide a more dynamic, decentralized environment for exploiting vast user bases while evading traditional security measures (Elezaj et al., 2021). In Blackhat Resources channels, users frequently engage with the content by providing feedback on the effectiveness of various hacking tools. They share both positive and negative experiences, which helps other members make informed decisions about which tools to use. For instance, a user commented, ”i was not able to download it before,” indicating a problem with a specific tool, while another might say, ”Try method 1 or 3 I hope REMCOS working,” suggesting effective methods.

What You Need To Know About Dark Web Telegram Chat Groups And Channels
Though the wild days of dark web sites like Silk Road are long gone, there remain many profitable illicit stores across the internet. Some of the most profitable are now running openly on Telegram, including the one that researchers say is the biggest of all time. Copyright media received 9,217 replies from 223 posts, while Pirated software attracted 20,069 replies from 1,319 posts. For flagged posts, the model categorizes the CAC and extracts URLs and executable files, which are then analyzed with VirusTotal and PhishIntention. Any flagged items are reported to security vendors, blocklists, and targeted organizations, identified using the 7+ Million Company dataset. Sign up for your free account today and start protecting your external attack surface from potential threats.

How To Search For Channels In TgramSearch
Additionally, in some of the communities beyond financial fraud there are a great number of these groups sharing about and boosting recent exploits. It also allowed for threat actors to communicate with each other and share other new or ongoing illicit communities. In recent years, Telegram has become a popular messaging platform for both illicit and legitimate communication activities. The app has allowed people from all over the world to be able to share and collaborate more than ever before. However, it has also allowed numerous dark web forums and other nefarious groups to move onto the messaging app as well and create illicit channels successfully. More recently, there has been a spike in illicit activities moving into online messaging applications like Telegram.
Top 6 Dark Web Telegram Groups And Channels In The UK
- Concerns regarding data handling also persist, and reports of user data being turned over to foreign authorities in Germany have raised concerns about privacy implications.
- With corporate devices, malicious actors can gain access into companies’ environments.
- This accessibility contributes to the platform’s role as a hub for illegal activities, enabling a diverse range of users to engage in covert operations.
- WIKILEAKS is also the result of the dark web.Dark websites don’t come up in search results when looked up on search engines like Google.
These hidden corners of the internet provide valuable insights into the activities of cybercriminals, making them essential resources for monitoring and staying ahead of emerging threats. Telegram won’t ever compete with cybercriminal activity present on underground forums in terms of scale but it will continue to be used for the fraudulent activity discussed in the previous posts. Its ease of use, reliability, and low barrier to entry also mean that it will continue to be used by the cybercriminal community active on more serious hacking forums when they need to communicate with the wider world. While Telegram is further down the hierarchy of serious cybercrime, the lines blur, and we do observe actors crossing from these more serious hacking forums into Telegram – and vice versa. Criminals on deep and dark web hacking forums use Telegram as an auxiliary communication platform, which we know because they discuss Telegram channels and share their handles in their forum posts.
The Hidden Danger Of Telegram CP (chat Groups And Channels): Exposing The Most Vulnerable
Instead of disappearing, Hydra’s network simply adapted to a new medium, underscoring the difficulty of suppressing illicit commerce with infrastructure takedowns alone. Although it monitors hacker forums, its coverage remains limited, as it does not track some of the key platforms listed in our Top 10 Dark Web Hacker Forums. Some chat groups trade tips on insurance fraud, credit card fraud or counterfeit money. One vendor offered a highly unique “revenge mail” service, sending a selection of different types of animal shit (horse, dog or cat) in a box to a name and address of your choosing for £20, although a cowpat costs a premium £25.
Law enforcement in Russia and Germany confirmed that Hydra affiliates were using Telegram bots to automate sales, effectively replicating market infrastructure in a mobile app. One of the main objectives of threat actors is to exploit the monetization potential of stolen information. By breaching the security of infected devices, they gain access to valuable data such as browser fingerprints and login credentials. Browser fingerprints are unique identifiers that can be used to track users’ online activities and potentially compromise their privacy.
A Massive Mobile Location Data Hack May Have Risked Gay People’s Safety
Flare integrates into your security program in 30 minutes and often replaces several SaaS and open source tools. With corporate devices, malicious actors can gain access into companies’ environments. Signup for PureVPN to get complete online security and privacy with a hidden IP address and encrypted internet traffic. PureVPN is the best-in-class VPN that not only provides you with digital freedom but also takes care of your digital security when you are browsing the web.
The platform’s design, which emphasises privacy and minimal regulation, has made it a favoured space for extremist groups. These groups exploit the app’s private channels to disseminate propaganda and recruit members, operating with reduced scrutiny compared to more regulated platforms. This use mirrors the dark web’s role in fostering extremist ideologies, providing a secure environment for the spread of harmful content and coordination of criminal activities. Despite having their Telegram channels shut down multiple times for violating platform rules, Dark Storm Team consistently manages to resurface and continue operating. Their resilience demonstrates how cybercriminal groups adapt and evolve, using Telegram as a critical tool for coordinating and executing attacks. There is an active demand for OTP bots, as many of these results displayed activity within minutes of the query.
BidenCash claims to impose fines or bans on suppliers whose listings are repeatedly found in public sources. While not a direct cyber threat, vx-underground serves as an educational resource, providing access to malware source codes, breach analysis, and cybersecurity intelligence. A widely recognized platform in the cybersecurity community, vx-underground is known for its extensive collection of malware samples, research papers, and cybersecurity insights. Often many of these types of attacks as a service type of criminal operations that are sold are still predominantly on dark web forums and marketplaces. For example, rarely has it been seen that the illicit communities on Telegram allow others to buy, sell, or trade other cyberattack methods such RaaS or other attacks as a service.
Dark Telegram Channels And Groups
Distributing pirated media is a serious offense actively banned by organizations and authorities alike to protect intellectual property rights (Greco, 2023). Detailed information about the quality of the video (such as the resolution, e.g., 720p, 1080p, 4K) was also provided.Similar to other CACs, there were several sources for distributing the content. 34.6% of the posts had the media as an attached file that could be directly downloaded by the user.
With 20,000 members, Moon Cloud shares a wide range of compromised data, including URLs, email addresses, IP addresses, passwords, and usernames. The analysis of Telegram’s black market showed that drugs are one of many illicit products traded on the platform. “Compared to darknet market use, Telegram is a lot easier to use and more convenient for buyers,” said Monica Barratt, a social scientist at RMIT University in Australia with an expertise in online drug markets. The messaging app has also become a key node of the drug trade in Russia, where it is used by narco bloggers who discuss different drugs and where to buy them, and increasingly in other countries such as Argentina.
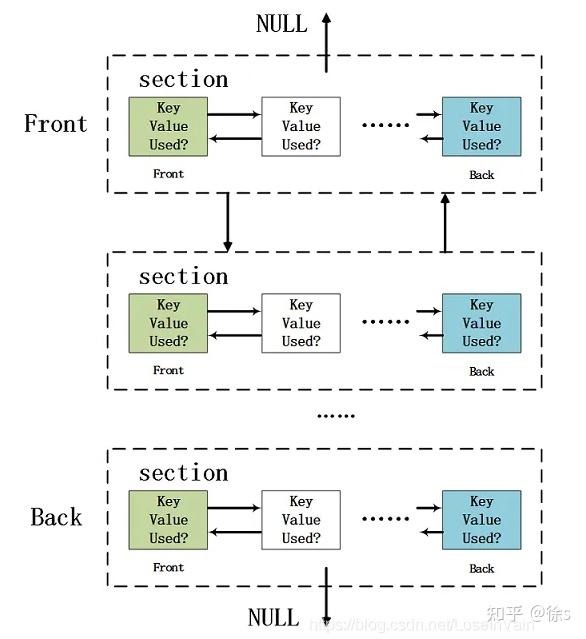
It also allows organisations to proactively detect security vulnerabilities and mitigate them before they are exploited. The activities within illicit communities on Telegram and dark web forums differ significantly when it comes to the buying, selling, or trading of cyberattack methods. While both platforms provide a haven for illegitimate online activities, Telegram tends to have more restrictions in place. In their bio, they describe themselves as “the largest and most versatile cloud on Telegram”, where logs extracted from other cybercrime channels are posted for easy access. Their operation is based on a mixed model—offering both free and paid services—and they claim to add more than 2,000 new logs daily, collected from various sources, including specialized malware like LummaC2 and Stealc. With cybercriminals finding new ways to breach databases, install ransomware, and otherwise harm your business, keeping up with cybersecurity trends is crucial.