
Just remember, if you want to explore the dark web, be very careful. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device. Tails is a mere 1.3 GB download, so on most connections it will download quickly. You can install it on any USB stick that has at least 8 GB of space. Tails works on most computers manufactured in the last 10 years.
During this process, your ISP can still see that you’re using Tor because the entry node is now fully visible. Not to mention the entry node will see your IP address, so if it’s compromised, a hacker would be able to get a hold of it. More importantly, even the VPN service will now see what you’re doing inside Tor. Just for laughs and giggles, we visited this random pug’s ultimate guide to the dark web. You’ll notice that some websites’ loading times are longer when using Tor. If you decide to venture into the dark web, be sure to educate yourself on the potential risks and dangers.

Legal And Ethical Considerations
- The use of the dark web usually means that you are attempting to engage in activity that you could not otherwise carry out in the public eye.
- Social platforms buzz with anonymous conversations, even as law enforcement hunts through digital shadows to crack down on criminal rings.
- Internet security software like Kaspersky Premium are comprehensive to cover both identity monitoring and antivirus defenses.
- While the dark web is often depicted as an anarchic forum for criminal activity, that’s not necessarily true.
This is the main way that search engines become aware of a certain website or web page, and is generally how sites like Google add web pages to their index. If the signal goes through the Tor network first, your ISP will be able to see that you are attempting to connect to a Tor node. Though no one should bat an eye just because you’re attempting to access the dark web, keep in mind that in some countries, like the United States, even a simple foray can get you in trouble. Next step – your request will be transferred to Tor entry nod which in turn transfers to one or more Tor relays. Afterwards, your request will be matched with the appropriate website. Tricky, but effective; that’s why it’s, by far, the best method to access dark web content.
What Is The Dark Web? Myths, Realities And Cybersecurity Risks
You won’t be able to access .onion addresses using a standard search engine as they aren’t indexed by crawlers. As search engine crawlers do not catalog these pages, you would need to know the exact link to access a website in this area of the internet. This could include government services to access your records, health care services, members-only areas, intranets, or corporate resources. Surfshark supports unlimited simultaneous connections to protect as many devices as possible. Also, try its services risk-free with the 30-day money-back guarantee.
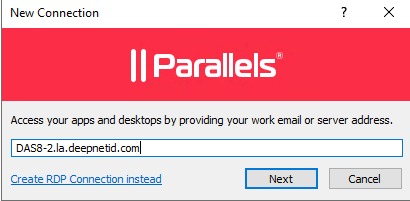
Please Continue The Installation Of Brave In The
Overall, Subgraph OS is a secure and privacy-focused operating system well-suited for high-risk environments. Additionally, you can opt for Subgraph OS as a second option to Tor. While it might appear tempting to venture into the dark web, it’s crucial to understand that the risks here are far more severe compared to the deep web. Therefore, if you do decide to explore it, exercise extreme caution. As listed above in our article, even respected organizations like the BBC and ProPublica have a version of their site on the dark web.
Use A VPN
While operational, the Silk Road was the hub for various illegal transactions. Since the site ran on Tor, which granted a high level of anonymity, users could trade weapons, hard drugs, and other illegal substances. Payments were primarily in bitcoins, further contributing to the site’s safety and security.
Why Use Tor?
Cybersecurity Student → Conducts research on privacy tools → Accesses ethical hacking forums (legal) using Tor. Journalist in India → Uses Tor to access a whistleblowing portal → Submits information anonymously while protecting their identity. Install AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Download AVG Secure VPN to encrypt your internet connection and protect your privacy wherever you go on the web. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
- However, Bitcoin’s relevance in the digital world has also made it a scam target.
- Instead of simply routing traffic, Freenet stores encrypted chunks of data across nodes.
- People mostly use it for covert communication, anonymous tips submission, and stuff like that.
- Regardless of being a business, parent, or any other user of the web, you’ll want to take precautions to keep your information and private life off the dark web.
- Just turn on your VPN, wait for the connection to stabilize, and launch Tor.
If you’re lucky enough, you can find it on clearnet privacy forums. The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. You can choose the best darknet (.onion) website that suits you and start surfing.
News, Media, And Other Information Organizations
While this doesn’t tell the exit node what your original IP address or your geographical location is, it could spy on your activity if the website you’re visiting isn’t a secured HTTPS website. Like I2P, Freenet is a self-contained network within the network that can’t be used to access sites on the public web. It can only be used to access the content uploaded to the Freenet, which is a peer-to-peer distributed data store.
Best Practices For Staying Safe
Conventionally, Nord also doesn’t log your data and uses AES 256 encryption. While this is good advice for any type of web browsing, be particularly careful not to offer up any personal details, such as your credit card info or email address. Use cryptocurrency to buy anything, and use a disposable email address for any type of communication on the dark web.
Some common pain relievers and sleeping pills available in the EU are illegal in various Middle East and Asia countries. Terrorist groups have used the dark web since its inception due to its anonymity and lack of regulation. The dark web provides these groups with chat platforms to inspire terrorist attacks and ‘How-to’ guides to teach people how to become terrorists and hide their identities. The urban legend of ‘Red Rooms’ that features live murders has been debunked as a hoax.
Naval Research Lab as a system of decentralized, anonymous nodes to enable anonymous online communication. Standard search engines index these websites and are accessible without special configuration. Being hidden doesn’t translate into being completely protected from the possibility of tracking, or, when it comes to illegal activities, of risk. However, it’s up to us to take control of our personal privacy in a world of bulk data collection, surveillance, and personalized ad tracking. To access a dark web resource, you will need to know its web address to the letter. These websites will also use .onion top-level domain names, and many of them will be very long, random combinations of letters and numbers.
Deep Web Search Engines
The dark web is infamous for containing sites such as Silk Road and other marketplaces where users could potentially buy drugs and/or weapons, stolen credit cards, IDs, and much more. The majority of the web is called the “deep web” (often referred to as the “invisible” or “hidden” web). The deep web is basically all the content that you can’t find using Google or Yahoo search. So, that means that the number of pages increased by over 100 trillion in just over three years. Hypothetically speaking, Google may be aware of well over 200 trillion individual pages (these are obviously NOT all indexed in the search engine).
Keep in mind that many criminal organizations use the dark web to communicate or sell merchandise. You may very well end up in the middle of a stakeout that could turn ugly. So, if the website looks fishy, close the tab, and forget about it.



