Together, we can create a united front against the darknet threat landscape. Explore the vast array of illegal goods and services available on darknet markets, where you can stumble upon a world filled with unimaginable offerings. In this article, we’ll explore the rise of these illicit online marketplaces and their impact on society and economy as a whole. From illegal goods and services to the consequences faced by both buyers and sellers, we’ll uncover the dangers lurking in these virtual underworlds. Brace yourself, because we’re about to take you on a journey through the perilous world of darknet markets.

While our results may not be exhaustive, we believe the security mechanisms implemented by the market interact somehow with potential market closures. That is to say, markets that want long-term stable operations will pay close attention to user experience and security. We exclude impounded retirement and voluntary retirement because these two reasons for closure are often affected by more complex factors 22, 35. This weakness would make them more prone to being disrupted by a third party. This would often result in the loss of data and trust, which in turn might encourage users to switch to competitor markets. In a narrow sense, the term “dark web markets” meant a marketplace on the Tor network.
Darknet Market Vendors Turn To DeFi
Monero is the most popular and valuable AEC, but other top coins include ZCash (ZEC), Oasis Network (ROSE), Secret (SCR) and Decred (DCR). At the time of its retirement, White House Market had 48,679 active listings on its website. Since then, it appears Dark0de grabbed the #1 spot, with an impressive 69,103 active listings. Only download files through Tor if absolutely necessary, and always double-check the validity of any .onion links before accessing them.
Equity Group Posts 17% Profit Growth To KSh 346 Billion As Transformation Strategy Gains Momentum
Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional. New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve.
Financial Markets, Financial Institutions, And Fiscal Service
After all, for betweenness centrality we rely on the fact that the user exists on many shortest paths, and is less reliant on its specific position in the path. For a vendor, this in turn might imply that they or their products are often discussed and that the vendor actively engages with their clientele, all of which may promote their sales. Thus, a high directed weighted betweenness centrality can be interpreted here as a good indicator of vendor success. We note that preliminary results showed this variant to also have the best performance. Betweenness centrality30,31 measures the extent to which a node is on shortest paths connecting pairs of nodes in the network. In other words, it measures how important a node is with respect to connecting various communities in the network.
The Increasing Risk Of Data Breaches
Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. Significant technological innovations and trends have reshaped dark-web marketplaces over recent years. In 2025, many platforms have adopted decentralized architectures, reducing single points of failure that previously made them vulnerable to law enforcement takedowns.
- The whole process is integrated with the market and is done on a case-by-case basis.
- Finally, the “Methods” section provides more in-depth descriptions on the dataset and network extraction as well as the activity indicators, network measures, and evaluation metrics used in this work.
- Russian Market has operated since 2019, specialising in stolen credentials, stealer logs, and remote desktop access.
- Furthermore, although a vendor’s sales volume is merely a proxy for their trade volume, we may reasonably expect those with the largest trade volume to be among the top vendor percentile in terms of sales.
- In addition to providing criminals with a platform to conduct transactions, Parsarad laundered virtual currencies for narcotics traffickers and cybercriminals active on Nemesis.
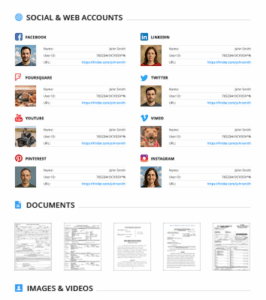
The Dark Web Privacy Dilemma: Linguistic Diversity, Talkativeness, And User Engagement On The Cryptomarket Forums

These efforts help folks learn how to secure their personal information, recognize suspicious activity, and take preventative measures. What makes these marketplaces particularly tricky is the level of anonymity they provide; both buyers and sellers use encryption methods to protect their identities and transactions. For instance, cryptocurrencies like Bitcoin are commonly used for payments because they offer a degree of anonymity. In response, darknet market vendors are increasingly shifting their financial activity toward decentralized platforms. Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. Dark markets continually adapt and evolve to stay ahead of law enforcement and security measures.

Darknet markets will increasingly use decentralized technologies (e.g., blockchain, Freenet) to evade takedowns. Defenders must integrate machine learning for real-time anomaly detection in encrypted traffic. In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described. Once the buyer confirms satisfaction, the funds are released to the seller. PageRank computes the probability that a random walker, that follows one of the available neighboring edges or jumps to a random node with a particular probability, ends up at a given node.
Thus, a high in-degree in our networks indicates many different users responding within a relatively short time frame or responding in a topic they started. Since it is likely that those that respond shortly after a post have seen that post, a high in-degree implies visibility to many different users, thereby improving the aforementioned brand awareness. As brand awareness promotes trust and sales22,23 and trust is a good predictor of vendor selection24, a high in-degree might serve as a good predictor of vendor success. Privacy-focused cryptocurrencies like Monero have continued to proliferate across darknet markets since 2022.
Key Support Areas
Note that we rely on all data prior to the given month and not only the most recent month(s), because a vendor’s reputation plays an important role in their success and is based not just on the most recent activity. Details on the network extraction process and the computation of monthly sales statistics are provided in the “Methods” section. On the other hand, the implementation of security mechanisms reflects the operator’s business philosophy, even though this may change at any time. In the Bohemia market, there was betrayal and division within the operations team. However, not long after (August 2024), the dark web community believed that law enforcement agencies arrested the administrator(s) based on a news report 7, 25. Nevertheless, according to information from law enforcement agencies 31, the founder of the market was arrested a few months later.
This situation is, in addition, accentuated by the increased frequency of competitors’ attacks against each other. Monitoring active marketplaces offers early access to malware kits, credential dumps, and fraud tools. Tracking vendor migration—such as from Archetyp to Exodus—provides insight into tactical shifts. Focusing intelligence collection on specialised marketplaces yields better ROI for threat detection and proactive defence. By 2026, darknet markets will likely integrate quantum-resistant encryption, complicating takedowns. Cybersecurity training must adapt to include post-quantum cryptography and AI-augmented threat hunting.
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from … Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal…
La Face Cachée De La Cybercriminalité
All research articles published in The Indian Journal of Law and Legal Research are fully open access. Articles are published under the terms of a Creative Commons license which permits use, distribution and reproduction in any medium, provided the original work is properly cited. During our research, we noticed that there is a market where the product listing data can be obtained by submitting a single request to the server API.