While Tor offers anonymity on the dark web, your online activities leave breadcrumbs that can reveal your identity. That is why you should only use a reliable VPN like ExpressVPN or NordVPN for additional security and privacy. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential.
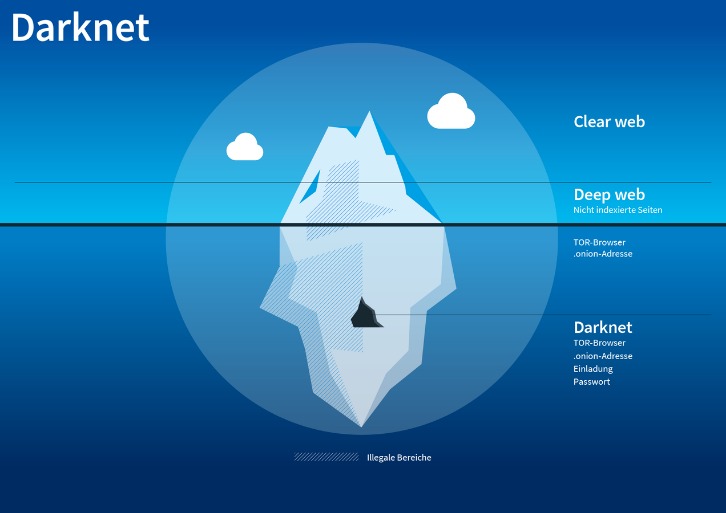
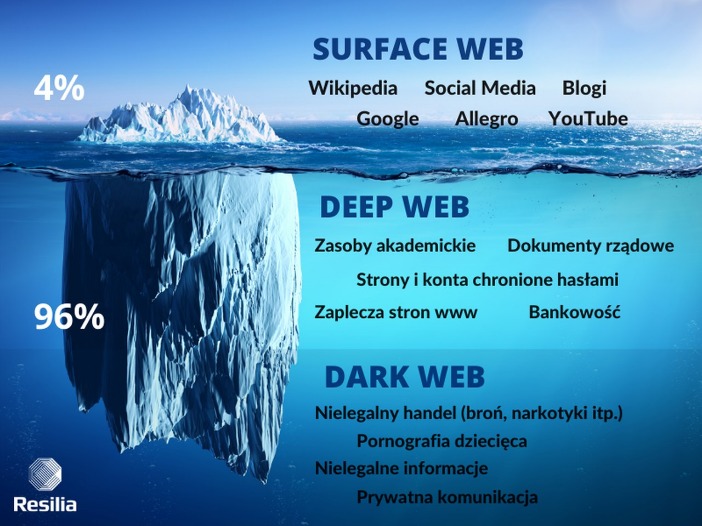
The dark web is a part of the deep web that contains websites not included in the mainstream search engine index. Lastly, to stay up-to-date with the happenings on a particular dark web website, forums are set up as a hub for information exchange. It can’t provide solutions should users encounter issues while using the website.
Newsletter
- For security reasons, we don’t display full onion addresses publicly.
- Unlike traditional TLDs, servers using the onion TLD are more difficult to locate.
- Due to the privacy-forward ethos of the Tor project, Tor Metrics stresses that the data it collects must not undermine the anonymity or security of the network.
- For anyone interested in exploring darknet trading, relying on comprehensive and current darknet markets list and verified darknet markets links is the best way to stay safe and informed.
When you use it, all the web traffic automatically routes through Tor. If the operating system detects any non-anonymous connection, it blocks it, thus ensuring maximum online protection. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net. In 2013, the FBI shut down the Silk Road, but it was later relaunched in 2014 with the new name of Silk Road 2.0, but the German authorities shut it down in the same year.

Top Dark Web Markets List: History, Evolution, And Current Landscape (
Anything from planting malware and stealing sensitive files to hijacking email accounts or breaking into social media profiles. The site gives out free samples of the stolen data every now and then to gain more customers. It also uses a strict authentication process to deter scammers. With its fast rise to fame and focus on money fraud, it’s no surprise that cybersecurity experts are keeping a very close eye on this one.

Which Darknet Markets Accept Zcash

If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers. Keep in mind that visiting the dark web isn’t illegal, but engaging in criminal activity there is. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
Explore Dark Web Marketplace Links With Confidence
Looking for an email from an edgy domain like email protected? Pissmail is the service for you, offering an onion based web service accessible via Tor browser. SimplyTranslate is an onion based language translation service using the google translate engine. It’s an easy and simple way to de-couple your internet usage from Google’s monopoly over the web.

You should never use your personal information on the dark web anywhere else in your life. In fact, create new throwaway accounts and documents if possible. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Avoid using payment methods that can easily expose your identity. The US Naval Research Laboratory developed The Onion Routing (Tor) project in the late 90s. A network browser gives you access to sites with the ‘.onion’ registry operator.
Security Upgrades
Monero’s ring signatures, stealth addresses, and RingCT ensure untraceable trades. In 2025, 95% of markets prefer XMR over BTC’s public ledger, with transaction volume up 60% since 2023. Today’s markets reflect a decade of evolution, balancing user demand with operational security against an ever-present cat-and-mouse game with authorities. However, any illegal activities conducted on the dark web, such as purchasing illicit goods or engaging in criminal behavior, are still punishable by law. The market emphasizes anonymity and security, conducting transactions exclusively through cryptocurrencies like Bitcoin and Monero.
Recommended Practices For Safe Darknet Transactions
It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. Launched in 2020, Cypher Marketplace sells fraudulent documents, stolen credit cards, fake IDs, and malware. Its emphasis on user anonymity and document forgery makes it a core tool for identity fraud. Alright, let’s get into the meat of it—the darknet markets that are ruling 2025. I’ve been poking around these places for a while now, from the giants like Abacus to the old-timers like Vice City.
The readers like you support Beencrypted to help keep up the good work. When you purchase using links on our website, we may earn an affiliate commission at no extra cost to you. To use social login you have to agree with the storage and handling of your data by this website. XMR hides transaction details, unlike BTC, which dropped 40% in use due to tracking risks since 2023.
Chatbot Security Measures You Should Know About
They take BTC and Monero, and the site’s got a sharp, modern look—vendor profiles are loaded with ratings and reviews, easy to skim. What’s dope is their forums—real talk, not just noise—building trust like Telegram’s side hustle vibe. Escrow’s standard, keeps things fair, and I’ve never seen it glitch out. For 2025, they’re hyping a peer-to-peer escrow twist—could cut out middlemen and shake up how deals flow, which I’m stoked to see play out.
Shuttered Markets And Lessons
They really don’t care about the loss and dilemma of the victims whose data has been stolen. These markets are a hot spot for selling stolen personal data. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information. The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses.



