
Ethical concerns arise when one considers that fraudulent behaviors normalize deceit, creating an environment where dishonesty is increasingly accepted or justified, gradually eroding societal values. Ultimately, the severe legal and personal consequences far outweigh any perceived short-term advantages, underscoring the high-risk nature of using fraudulent identification documents. The Dutch National Police’s operation against Hansa Market in 2017 illustrates this approach. They seized control of the market’s servers and continued operating it covertly for weeks, gathering extensive intelligence on vendors, buyers, and operational networks before shutting it down permanently. We think blackpyramidmarket.com is legit as we found few indicators which might point to a scam. Blackpyramidmarket.com review resulted in a trust score of 71.
IDENTITY AUTHENTICATION

Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Markets like Perico represent the next wave — safer for vendors, harder for law enforcement to trace, and accessible only to privacy-savvy users. For cybersecurity professionals, journalists, and policymakers, understanding how these systems evolve is crucial to monitoring and mitigating the impact of underground economies.
The Escrow Process

It has built a reputation for being a reliable source of stolen credit card data and PII. Renowned for its extensive inventory of financial data and sophisticated operating methods, Brian’s Club is a key player in the underground economy of financial cybercrime. People use dark web marketplaces for all sorts of reasons. Some are looking for illegal stuff they can’t buy elsewhere, like drugs or counterfeit documents. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials.
Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers. Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Learn how darknet markets function and the challenges they present to cybersecurity, shedding light on the hidden side of the internet. To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers.
Cyber Team: Offensive Hacking Services (Offline)
However, the website has some security risks, and users experience glitches. However, in April 2022, this site went offline after American and German federal government law enforcement agencies seized the website servers. Some alternative links are available, providing access to the marketplace. It’s recommended not to use new alternative links as they could just be planned exit scams. Researchers from iProov’s biometric threat intelligence unit have uncovered what appears to be a simple yet simultaneously sophisticated identity protection bypass operation being implemented on the dark web.

Blitz Malware: A Tale Of Game Cheats And Code Repositories
We’ll also discuss examples of major marketplaces, myths about the dark web, and tips on staying safe in case your personal data ever ends up there. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web. These sites often look basic or outdated, and their URLs are lengthy strings of random letters and numbers.
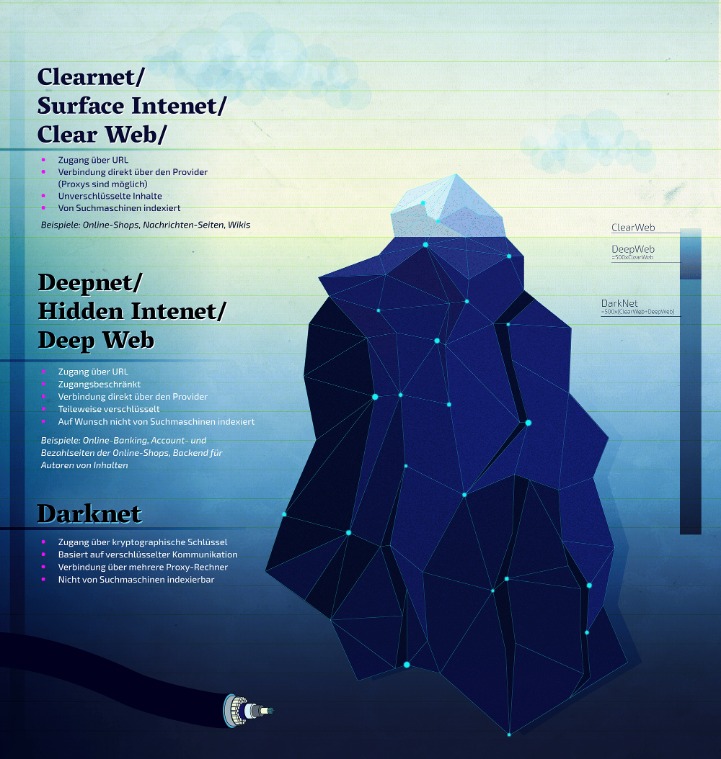
Any site that ends with .onion can only be accessed through TOR. Unlike traditional TLDs, servers using the onion TLD are more difficult to locate. This makes it more difficult for authorities to locate and take down these sites. The clearnet is the regular internet you’re used to using, where network traffic origins are fairly easy to pinpoint. The Silk Road was the first popular DNM which appeared on the scene in back in 2011. Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more.
- It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data.
- The process is structured similarly across most dark-web marketplaces and generally includes using privacy-focused cryptocurrencies, anonymous communications, and secure delivery methods.
- The market claims to provide secure and anonymous commerce services.
- The market frequently makes headlines for releasing massive troves of stolen data, often as a way to advertise its services.
- The buyer purchases and moves Bitcoins to the darknet user account used by the buyer and makes the desired purchase.
- Transactions in these underground markets prioritize anonymity and security to evade detection.
Explicit And Illegal Content
Another tor website that lets you purchase EU cards, US cards and PayPal accounts with Bitcoins. If you want to Email/chat/discuss about something with strangers or your friend anonymously and looking for dark web links of tor chat & email services, then you will find below dark web sites links helpful for you. Digital Goods, Drugs, Fraud and Guides & Tutorials categories have a large no. of listed products on Elysium Market. This darknet market offers simply UI but there is no advanced search bar like Drug Hub.

Darknet Markets Links
The dark web market changes all the time, but some dark web marketplaces have made a name for themselves as the biggest and busiest spots. These sites attract thousands of users every day, offering all kinds of illegal goods that keep the underground trade going. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
The Multi-Layered Mitigations Required To Fend Off Evolving Dark Web Identity Attack Resources

Choices of currencies are EUR, USD, CAD, GBP, CNY, AUD, CHF, RUB, and SGD. It offers gift cards, Debit cards, CC dumps, cash flip, counterfeit, laundering, crypto flip, mixing and hacked wallets. PayPal accounts are listed with account balance, account price, your profit and account location. Along with order, you get a free cashout guide and socks5 proxies. Available cloned credit cards are Mastercard, CCV, US VISA, and VISA. When comes to shipping, it provides free and Express shipping.
It uses PGP encryption, two-factor authentication, and OPTP authentication to ensure users’ security. It’s a place people go to buy and sell illegal goods and services, from drugs to illegal weapons to tools for fraud, and worse. A Canadian market established in 2021, WTN offers over 9,000 products, including narcotics, fake goods, and digital services.
The U.S. Army developed “onion routing” to protect intelligence communications online. As you can imagine, bad actors around the world would be attracted to any method of keeping their illegal activities undercover, and began to appreciate the dark web as a place to more or less safely conduct their activities. Later on, the underlying Tor code was released into the wild under a free license, leading to the formation of the Tor Project. In 2008, the first Tor Browser was released, making it easier for any internet users to access the dark web.
So, once you’ve activated your VPN and your privacy is secured, it’s time to visit Tor’s official download page. Instead, you need to get the Tor browser to access the dark web. Make sure that when you download the Tor file, it’s from their official website.



