Keybase is an exciting identity service that aims to make it easy for you to link the presence of your online identities together in a cryptographic way. You can upload your PGP key or have the site create one for you, and use it to cryptographically link your Twitter profile, Github account, or Bitcoin address together. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results.

What Types Of Marketplaces Can You Find On The Dark Web?
Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. Dark web websites look pretty much like any other site, but there are important differences. Instead of ending in .com or .co, dark web websites end in .onion. That’s “a special-use top level domain suffix designating an anonymous hidden service reachable via the Tor network,” according to Wikipedia. Browsers with the appropriate proxy can reach these sites, but others can’t.
It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally.
Is It Illegal To Access The Dark Web?
To understand the realities of the hidden internet, better grab a flashlight. A lot of illegal activity occurs on the dark web, and onion websites are popular hangouts for cybercriminals and scammers. But if you use antivirus software, avoid clicking shady links, and stick to known sites you should be okay. It’s also a good idea to set up a VPN for an extra layer of protection. ProtonMail is a Swiss-based encrypted email service that doesn’t require personal information when you sign up. ProtonMail’s end-to-end encryption makes it one of the best onion sites for easy-to-use, secure, anonymous email.
Why Can’t I Access Onion Sites?
The marketplace has a simple interface, lets users filter logs easily, and accepts Bitcoin, Monero, and Litecoin for payments. You can even find things such as BIN checkers and PayPal cookie converters. Another reason the Russian Market is so popular is that it’s pretty inexpensive compared to other dark web marketplaces. Now, that is not to say illegal behavior is completely beyond detection. The dark web combines encryption, anonymity, and hidden doorways to provide the perfect sanctuary for such illicit activity compared to the usual internet, which is more vulnerable and trackable.

Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
In fact, everything is in English, and the site picks up users everywhere in the world. People visit this market to buy stolen credit cards, personal data, remote desktop account credentials, and logs gathered from information-stealing malware. Brian’s Club has been around since 2014 and remains one of the most well-known credit card shops on the dark web. It sells stolen card data — dumps, CVVs, even wholesale batches — and lets users bid on fresh leaks.
The Best Tor And Onion Links
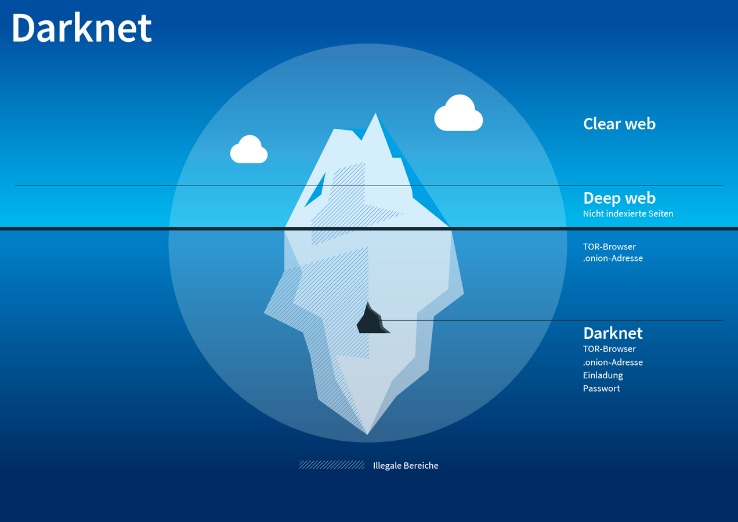
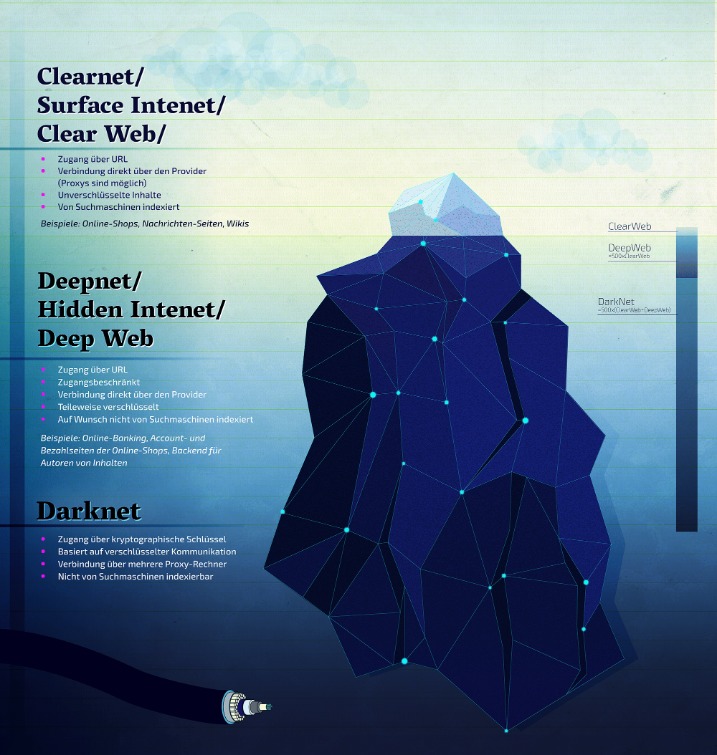
While the deep web comprises about 90% of the total web, the dark web makes up just a tiny fraction of the deep web total. As noted by Andy Greenberg at Wired, while the deep web makes up approximately 90% of the internet, the dark web makes up only around 0.1% and is designed to provide anonymity for users and site owners. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. There’s a significant risk to dark web users of being exposed to malware (malicious software) infections. There are several programs that hackers frequently use on the dark web. The dark web is also a place for scammers to attract vulnerable and unwitting victims.
POPULAR POSTS
- It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
- For example, DuckDuckGo is the most popular but often shows repetitive results and is sometimes unrelated to the question.
- The fallout for victims whose data is stolen and sold can be devastating.
- On top of that, the provider offers perfect forward secrecy (PFS).
- This platform has rapidly become a key player in the fraud market, trading in PII and SSH credentials while making use of both the clear and dark web.
- However, it has a sneak peek, easy guide steps, and/or a quick list providing quick in-page navigations and easily-found answers if desired.
Tor anonymity comes with a cost since malicious hackers and criminals like to operate in the shadows. For example, perpetrators of trafficking and cyber attacks use the dark web to disguise their actions. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. Furthermore, it’s critical to understand that Whonix is not a stand-alone browser.
Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. The good news is that the platform will not see what you copy/paste. Your data is encrypted in the Tor browser before reaching the ZeroBin servers.

The BBC’s international edition Tor version is available on the dark web, giving access to unbiased news in regions where the BBC is blocked or censored. We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats. With over 20 years of experience in cybersecurity and marketing, Ben has held leadership roles at companies like Check Point, Cognyte, Cylus, and Ionix. Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Ransomware and cryptocurrency-based crimes saw a significant increase in 2023, with a nearly $176 million rise compared to 2022.
History Of Darknet Markets
The so-called darknet or dark web is a part of the internet that can be accessed only by specialized software or hardware and contains clandestine websites not found through normal search engines. DeepDotWeb was a regular searchable website that provided a directory with direct access to a host of darknet marketplaces selling illegal narcotics including fentanyl, cocaine, heroin and meth. Activities on dark-web marketplaces are closely monitored by international law enforcement agencies. Purchasing or selling illegal goods—such as controlled substances, counterfeit documents, or stolen data—can result in significant legal penalties, including fines, criminal charges, and imprisonment.
As a user or cybersecurity professional, approaching these marketplaces demands utmost caution, thorough knowledge of operational security, and constant awareness of legal boundaries. Understanding both the benefits and dangers ensures safer interaction and more informed decision-making in an ever-changing digital environment. By consistently applying these straightforward security tips, you can significantly mitigate risks and better protect your privacy, finances, and legal standing when interacting with dark-web marketplaces.

Hence, it should be the top priority to track these platforms and shut them down as quickly as possible. As we mentioned earlier, not everything sold on dark web markets is illegal. As terrible as its reputation may be, some vendors sell legitimate goods or services.
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. For instance, cybercriminals can buy credit card details with a $5,000 balance for just $110. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. While this topic may seem distant for most people, understanding how these spaces operate is crucial. It helps us stay more vigilant, better protect ourselves, and make informed decisions online. For several years, Yahoo was at the apex as the internet’s best web service provider, offering…



