And with the recent MimbleWimble (MWEB) upgrade, my admiration has only grown because I feel like it was exactly what Litecoin needed to become the ‘perfect money’ for the internet. Get the latest in privacy news, tips, tricks, and security guides to level-up your digital security. This method is called Tor over VPN, and it’s a great way to increase your privacy over using Tor alone.
Top Markets
- Litecoin is known for its fast transaction times and low fees, making it an attractive option for those looking to conduct quick and inexpensive transactions.
- It brings in vendor reviews from other places and verifies them using PGP signatures, so buyers can feel a bit more confident about who they’re dealing with.
- However, regardless of what the dark web favors will ultimately become the most popular coin and that’s something the community realizes.
- Like Bitcoin, Litecoin operates on a decentralized blockchain and facilitates peer-to-peer transactions.
- Brian’s Club is one of the best place to buy stolen credit card info, including CVVs, dumps, and even full account packages without revealing your identity.
- Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit.
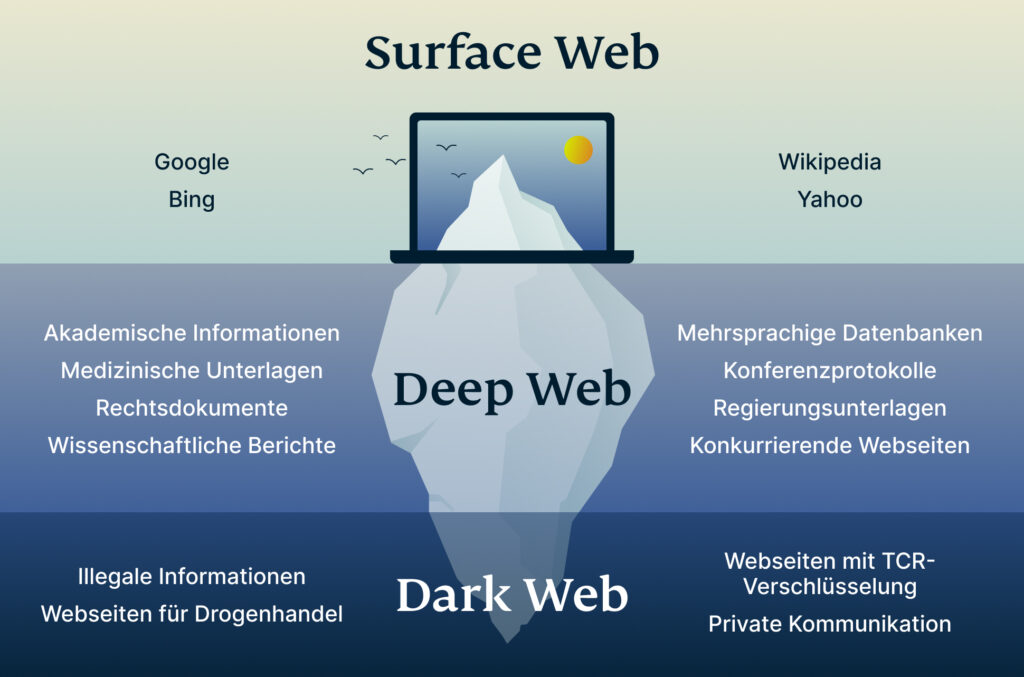
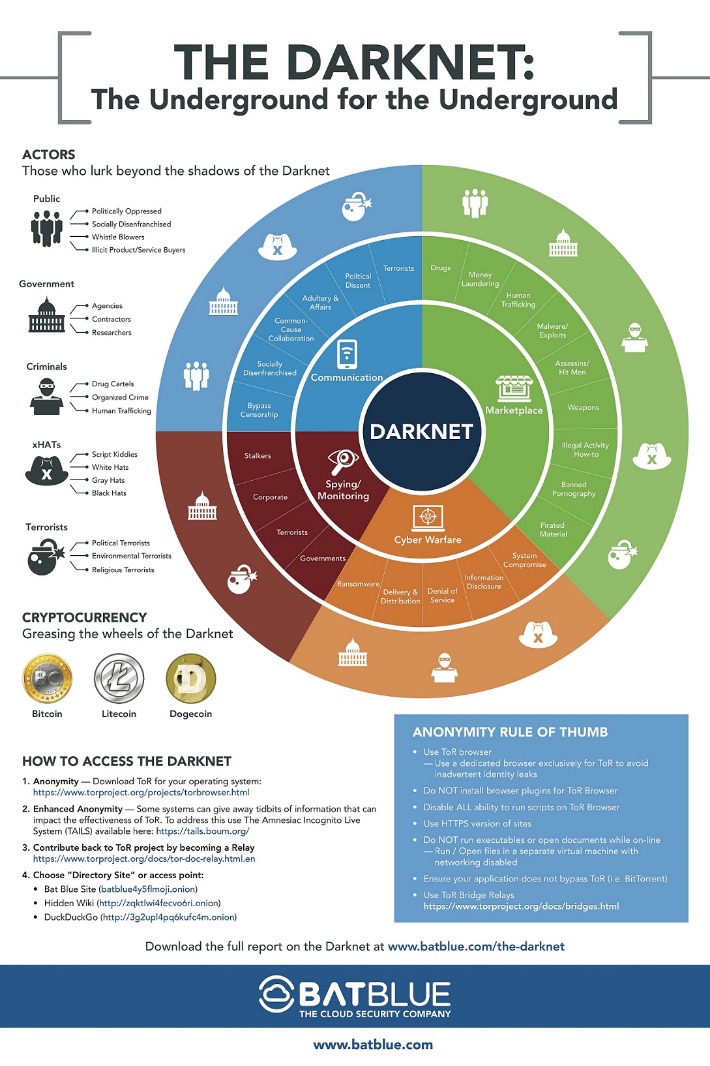
When using cryptocurrencies, individuals can conduct transactions without the need to provide personal information such as their name or address. This level of anonymity makes it difficult for law enforcement to track and monitor transactions, as there is no central authority overseeing the flow of funds. The use of cryptocurrency on the dark web offers convenience, trust, and anonymity to buyers and sellers. The adoption of privacy coins like Monero is increasing due to their non-traceability and lower transaction fees. However, it is essential to note that illicit activity represents only a small fraction of the overall cryptocurrency market.
- If any user is found not complying with the law, strict and immediate action will be taken against them.
- The dark web is where these coins are widely accepted unlike the real world where they are still taken more as a commodity than a currency.
- If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding.
- Launched after the takedown of AlphaBay in 2021, Abacus Market has rapidly risen to prominence.
That online zombie horde was capable of launching coordinated cyberattacks, cracking passwords, or mining hundreds of dollars a day worth of cryptocurrency. And by assembling that botnet from cloud accounts rather than hijacked computers, Ragan and Salazar believe their creation may have even been legal. Just because the seller has good reviews does not mean you can trust them. There’s nothing stopping sellers from packing up and leaving the market at any time. They could get a batch of bad products, get arrested before they can ship your order, or any other number of things.
The Future Of Renewable Energy Storage Technologies
Despite that I’ve used the recommended commission fees, my transactions have remained pending for the past three days, and my work has been paralyzed. In a conversation with Fortune, one of the report’s authors, Andrei Barysevich, provided additional details. According to him, Litecoin is popular because it has faster processing times as compared to bitcoin and can be stored in offline wallets. Cryptocurrencies are used on the dark web for anonymous transactions because they do not require personal information to be exchanged.

Security And Encryption
The darknet provides anonymity through the Tor network, but safety requires knowledge. Always verify onion links, use PGP encryption, and never reuse passwords. This directory lists only established markets with verified onion links. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data. It is a hub for financial cybercrime and offers a wide range of illicit services and stolen data that cater to sophisticated cybercriminals.
New Shamos Malware On Mac: Beware Of ClickFix Attacks
BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. The site allows users to find and buy a vast variety of products and services.
Why Are Darknet Markets Found On The Dark Web?
Using a reliable VPN provider helps keep you safe when you access marketplaces on the dark web. A VPN encrypts the data traffic and keeps your activities private on the dark web. It also masks your IP address, making it difficult for government agencies to monitor or track your activities. We recommend using NordVPN as it offers top-notch security features, including dark web threat protection.
As law enforcement agencies crack down on illegal activities on the dark web, money laundering schemes utilizing cryptocurrencies emerge as a growing concern. Cryptocurrency, particularly Bitcoin and Monero, plays a significant role in facilitating transactions for illicit goods and services. The most popular items purchased with cryptocurrency on the dark web are drugs, such as cannabis, cocaine, and MDMA. However, the dark web marketplace also offers a wide range of illegal offerings, including stolen credit card data, hacking tools, and counterfeit identities. While weapons are available for purchase, they represent a smaller market due to their accessibility outside of the dark web. Abacus Market appeared on the scene in 2021 and quickly became one of the heavyweights among English-speaking markets on the dark web.
Topics And Products Sold
This makes it incredibly difficult to find out who you are paying. Facebook is aware of attempts by many governments to restrict access to a tool that allows strangers across the web to talk and collaborate freely. While its .onion address doesn’t make it much easier to maintain an anonymous account, it does make Facebook more accessible in places where it’s censored. The internet’s favorite alternative to Google made a name for itself by not logging your search activity yet still providing decent results. This focus on privacy makes it the Tor Browser’s default search engine and one of the best onion search engines.

While these efforts aim to increase security and reduce illegal activities, they may also limit the privacy and anonymity that cryptocurrency offers on the dark web. The use of cryptocurrency on the dark web provides several advantages to both buyers and sellers. It offers convenience by allowing users to make anonymous transactions from the comfort of their own homes. It also fosters trust, as transactions are verified through the blockchain technology, ensuring that payments are made and received securely.
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. However, if someone were to pursue this, here are some safety strategies. This highly popular English-language market sold all varieties of narcotics. DNMs have a limited life and may be shutdown suddenly, leaving users with unfulfilled orders and sellers with no means of communication. The clearnet is the regular internet you’re used to using, where network traffic origins are fairly easy to pinpoint. Brand new marketplace for the Italian and International darkweb community after years of downtime.
Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation. Patterns recommended to avoid include hiring hitmen like Dread Pirate Roberts, and sharing handles for software questions on sites like Stack Exchange. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.